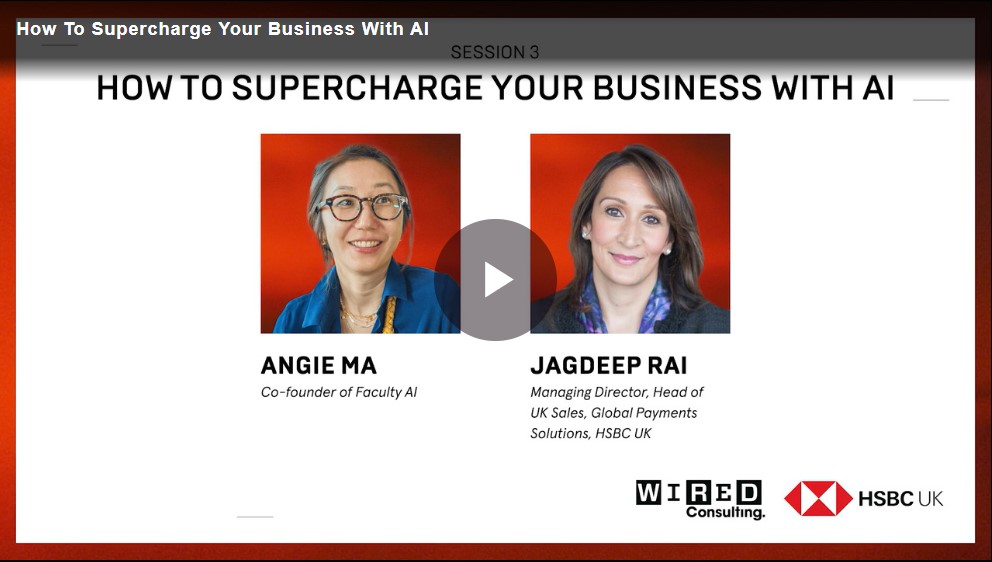
AI in action. Real stories. Real results.
Article

Although still early in its journey as an operational business, quantum gravity sensor technology s...








We can help you get your business started, and support you as your business grows. Access and manage your money with a range of business accounts, a business savings account and a business credit card.